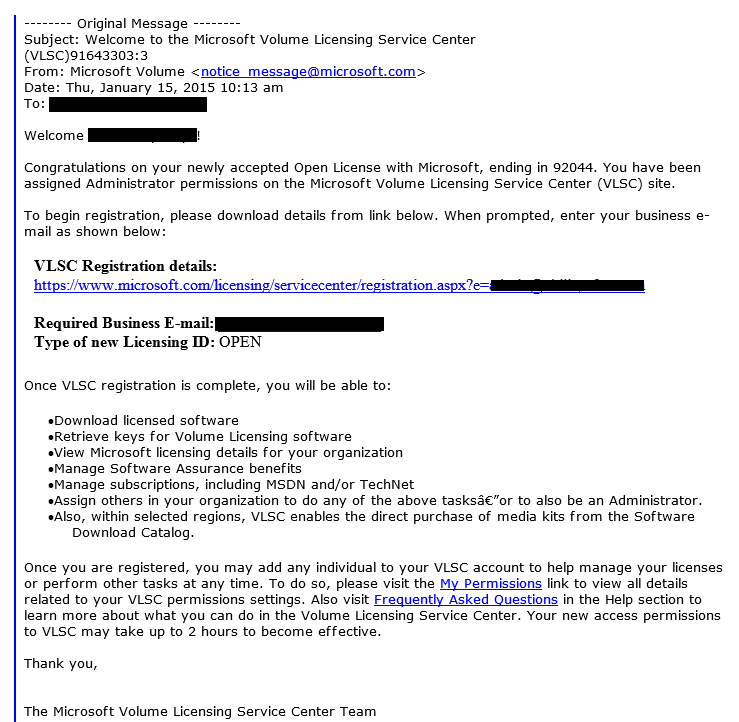
Stolen Laptops Lead to Nearly $2M in HIPAA Settlements
- Published in Security
- Written by Top Speed
- Be the first to comment!
- Read: 14613 times

Stolen laptops are a concern for every business - the loss of proprietary data, compromised employee or client information and concerns over access into the business's network, if they theft isn't reported right away to IT staff, are just a few of the ways a lost or stolen laptop can damage a business.
However if your business is in the Medical Industry the damage can be exponentially worse, as it was for two 2014 cases where the U.S. Department of Health and Human Services settled with two entities for total of nearly $2,000,000 USD as a result of potential HIPAA violations after laptops were stolen.
The first of the two incidents involved Concentra Health Services, who had an unencrpyted laptop stolen from it's Springfield Missouri Physical Therapy Center. During the investigation of this incident it was determined that Concentra had previously acknowledged via risk analyses that their lack of encryption on devices containing Electronic Protected Health Information (ePHI) was a serious risk. Concentra had begun the process of encrypting ePHI but the efforts had been "inconsistent" resulting in insufficient security in place to safeguard patient information. To settle these potential violations Concentra agreed to pay $1,725,220 and put in place an action plan to remediate these issues.
The second incident involved QCA Health Plan, Inc. of Arkansas, who reported in February 2012 that a laptop containing ePHI records of 148 individuals had been stolen from an employee's car. Upon investigation it was determined that QCA had failed to comply with multiple HIPAA rules with the beginning compliance date of April 2005 and ending June 2012. QCA Health Plan, Inc. agreed to pay a $250,000 USD settlement and was required to provide Health and Human Services with an updated risk analysis and risk management plan.
In 2014 we've covered some of the cyber attacks in the US and around the world; several of these attacks have involved the medical industry and include hardware theft and cyber attacks:
- February 2014 - Lost thumb drive compromises 3598 Texas Cancer Center patients
- February 2014 - Laptop stolen at St. Vincent's Indianapolis hospital, 1100 patient's information compromised
- February 2014 - St. Joseph Health System hacked, over 400,000 patients and employees personal information compromised
- February 2014 - Assisted Living Concepts had an incident of unauthorized access
- March 2014 - Franciscan Medical Group employees responded to a phishing scam
- April 2014 - Lubbock Cardiology Clinic had unauthorized access of their Electronic Health Record System
- April 2014 - Centura Health employees responded to a phishing scam
- April 2014 - Midwest Orthopaedics at Rush notified patients a doctor's email had been accessed by an outside individual
- May 2014 - DeKalb Health patient information exposed by "overseas hacking"
- July 2014 - Doctor's PharmaNet account accessed by unauthorized individual
- August 2014 - Community Health Systems reported the theft of 4.5 million patients information by cybercriminals
- August 2014 - StayWell Health Management experienced a breach affected personal information
- September 2014 - Central Utah Clinic in Provo may have had personal health information viewed by an intruder who broke in to one of their servers
- October 2014 - UC Davis Health System physician's work email was accessed by an unknown source
- October 2014 - Penn Highlands doctor's server was accessed by a "third party" intruder
- November 2014 - Jessie Trice Community Health Center patients information was stolen as a part of "an identity theft criminal operation"
- November 2014 - Onsite Health Diagnostics information was accessed and stored by an "unknown source"
- November 2014 - Central Dermatology Center notified patients that one of it's servers had been compromised by malware for roughly 2 years
- February 2015 - Anthem hacked, details still coming out
If the Concentra Health Services and QCA Health Plan settlements are any indication, many of these recent breaches may appear on the Health and Human Services list of settlements in the next couple of years. Add to that the information coming out from Anthem on their recent data breach of possibly 80 million subscribers information, the settlements could get even larger.
A few years ago a local doctor's office had an external hard drive assigned to an employee every night to be taken home. This seemed like common sense to protect the backed up company and patient data on the server in case of fire or theft. Unfortunately, one night this employee left the external hard drive in their car which was subsequently broken into (very similar to the Concentra incident). This doctor's office had to notify all their patients and employees of the loss and potential breach of their personal information. But all things considered this case could have been worse, had Health & Human Services been involved at the time this could have resulted in a business ending settlement or fine.
The important take away is if you're in the medical industry bound by the HIPAA laws now is the time to make sure you've done everything necessary to protect your business's and patients's data and avoid the chance of having to pay a large fine or settlement.